This guide is about the Instant Word Completion in Mac OS X with FI will try my best so that you understand this guide very well. I hope you all like this guide Instant Word Completion in Mac OS X with F5.
In many Mac OS X applications, you can activate a little-known word completion feature with a simple keystroke. This is incredibly useful for memorizing a word and diversifying vocabulary while writing, and has so many uses. It is quite efficient and easy to use.
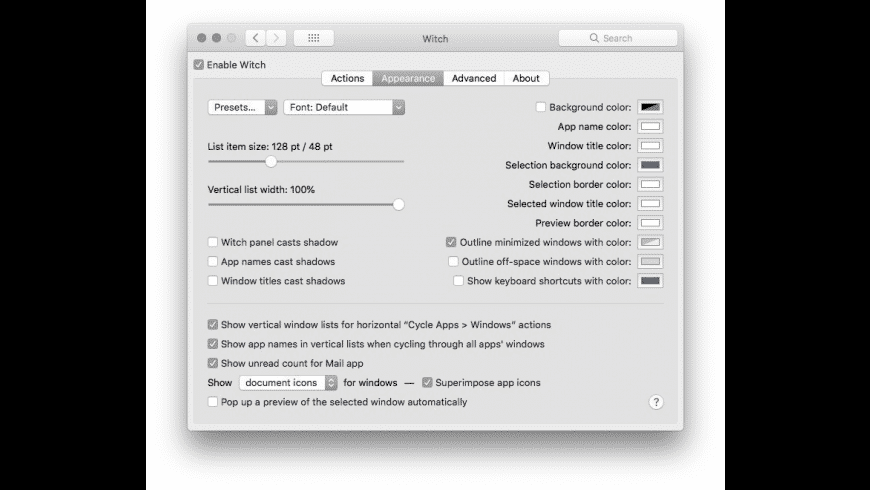
🐵 Below is a massive list of witch words - that is, words related to witch. There are 500 witch-related words in total, with the top 5 most semantically related being witchcraft, fairy, hex, glamour and warlock.You can get the definition(s) of a word in the list below by tapping the question-mark icon next to it. Have you been looking for a Mac OS X dictionary, that can translate any word from any language, for. In today's world, everything is digital. Switch back and forth between windows that don't belong to the same application using Witch in MAC OSX.
This is how this instant word completion feature works on a Mac, you can try it yourself with an app like Pages, TextEdit, Word, etc., which is recommended so you can experience how it works and how it responds to typed prefixes.
How to use Instant Word Completion in Mac OS X.
Start by typing the word and then clicking either F5 key or Escape key after you have written a letter or a few.
This simple keystroke brings up a large menu for each word, starting with the letter prefix you type, looks like this:
Word completion seems to be working just created by Apple’s Cocoa applications, so you can use the feature in Safari, Pages, Keynote, TextEdit, iCal, etc., but the Chrome browser, you will not succeed until the third-party applications developers decide to support feature.
This is really useful when you’re trying to remember how a word is spelled, or if you’re trying to think of words that start with a certain prefix or letter (scratch anyone?). If you’re wondering where a word list comes from, it’s tied to your Mac OS X dictionary, which is also easily accessible via a keyboard shortcut.
I knew you could do this with the Escape key, but I just learned from F5 to call the same perfect option. Thanks for the tip Ian!
This works on all versions of OS X and is separate from OS X auto-corrections and other word completion features.
Benefits: Instant Word Completion in Mac OS X with F5
- The Instant Word Completion in Mac OS X with F5 guide is free to read.
- We help many internet users follow up with interest in a convenient manner.
- The price of the Instant Word Completion in Mac OS X with F5 guide is free.
FAQ: Instant Word Completion in Mac OS X with F5
Guide about Instant Word Completion in Mac OS X with F5
A Witch's Word Mac Os X
How this Guide helping you?
What are the supported devices for this guide?
What are the supported Operating system?
Final note: Instant Word Completion in Mac OS X with F5
If you have any queries regards the Instant Word Completion in Mac OS X with F5, then please ask us through the comment section below or directly contact us.
Education: This guide or tutorial is just for educational purposes.
Misinformation: If you want to correct any misinformation about the guide “Instant Word Completion in Mac OS X with F5”, then kindly contact us.
Want to add an alternate method: If anyone wants to add more methods to the guide Instant Word Completion in Mac OS X with F5, then kindly contact us.
Our Contact: Kindly use our contact page regards any help.
On March 16, FortiGuard Labs captured a new Word file that spreads malware by executing malicious VBA (Visual Basic for Applications) code. The sample targeted both Apple Mac OS X and Microsoft Windows systems. We then analyzed the sample, and in this blog we are going to explain how it works, step by step.
When the Word file is opened, it shows notifies victims to enable the Macro security option, which allows the malicious VBA code to be executed.
Malicious Word File is Opened
Figure 1. Asks victim to enable Macro security option
Once the malicious VBA code is executed, the AutoOpen() function is automatically called. The first thing it does is read the data from the “Comments” property of the Word file.
Figure 2. The property “Comment” of the Word file
The value of the “Comments” is base64 encoded, which can be read out and decoded by the VBA code below:
After it’s base64-decoded, we can capture the code in plaintext, which is python script, as shown below.
Next, it takes a different route depending on the OS type, Apple Mac OS X or Microsoft Windows, that it is running on. You can see this in the the flow chart in Figure 3.
Figure 3. Calling different route according to OS type
We have found that this malicious VBA code uses slightly modified code taken from a metasploit framework which you can find at hxxps://github.com/rapid7/metasploit-framework/blob/master/external/source/exploits/office_word_macro/macro.vba
How it Works for Apple Mac OS X
As you probably know, Mac OS X comes with Python pre-installed by Apple. This allows it to execute python scripts by default. As you can see above, the base64-decoded python script is passed to the ExecuteForOSX function that is going to execute it at the bottom of the function (see Figure 3).
The python script is easy to understand. It extracts the code from a base64-encoded string, and then executes it. It is decoded below, and as you can see, it is a very clear python script.
When the python script is executed, it downloads a file from “hxxps://sushi.vvlxpress.com:443/HA1QE”, and executes it. The downloaded python script is a slightly modified version of the Python meterpreter file, which is also part of the Metasploit framework. The source code of the project can be downloaded from the following URL: hxxps://github.com/rapid7/metasploit-payloads/blob/master/python/meterpreter/meterpreter.py.
The major changes between the downloaded file (HA1QE) and the original file are the following:
Figure 4. Differences between HA1QE and meterpreter.py
The HTTP_CONNECTION_URL constant (hxxps://sushi.vvlxpress.com:443/TtxCTzF1Q2gqND8gcvg-cwGEk5tPhorXkzS0gXv9-zFqsvVHxi-1804lm2zGUE31cs/) is set to the Metasploit end-point that the script will be connecting to.
The PAYLOAD_UUID constant is used as an identifier for the client, which we believe is also being used by the attackers for campaign-tracking purposes.
Once the script is executed, it attempts to connect to the host “sushi.vvlxpress.com” on port 443. But at the time the request was made during our analysis, the listener (server) was not answering client requests.
Figure 5. Wireshark showing TCP retransmission error while connecting to the server
The python process remains active on the system while trying to connect to a reachable server.
Figure 6. Python script attempting connection to listener
How it Works for Microsoft Windows
Although the argument of the ExecuteForWindows function is as same as the ExecuteForOSX function, it does not use it. What it does instead is making a DOS-style command string starting with cmd.exe. When it is executed, powershell.exe is started without window (-w hidden), and it executes the base64-encoded code (-e base64-encoded code.) For more details, see the following screenshot.
Figure 7. Dos-style command
It’s base64 again. This malware’s author likes using base64 to encode the sensitive code. We will see more base64 encoded data in the rest of the analysis.
Decoding the base64-encoded data, we get the following powershell script:
The main job of the above powershell script is to decompress a piece of gzip data, which is in base64-encoded code, to get another powershell script (by calling FromBase64String() and GzipStream()) and execute it (by calling Start($s)).
Next, let’s move on to see the decompressed powershell code. To improve understanding, I modified some of the function and variable names.
Here is the code snippet:
From the above powershell code we can see that it first decodes the base64-encoded data. In fact, it is 64-bit binary code that is going to be executed later. Then, it allocates a buffer in the current process (powershell.exe) and copies the 64-bit code into the buffer by calling the VirtualAlloc and Copy functions. Finally, it calls the CreateThread function, whose thread function points to the new buffer. That means that the 64 bit code is the thread function and is executed. Based on our analysis, this malware only affects 64-bit Windows.
Figure 8. 64-bit ASM code
We analyzed the 64-bit code in IDA Pro, as shown in the above screenshot. Once it starts, it downloads a file from “hxxps://pizza.vvlxpress.com:443/kH-G5” into a newly allocated buffer. The downloaded file is actually a 64-bit DLL file. Before the thread function finishes, its stack return address is set to the newly allocated buffer that holds the downloaded 64-bit DLL. That means that the 64-bit DLL gets executed when the thread function is returned.
Next, we see that the DLL can communicate with its server, such as “hxxps:// pizza.vvlxpress.com:443/5MTb8oL0ZTfWeNd6jrRhOA1uf-yhSGVG-wS4aJuLawN7dWsXayutfdgjFmFG9zbExdluaHaLvLjjeB02jkts1pq2bR/”. We can see it in the debugger, as shown below.
Figure 9. Communication with its server
At this point, we are still working on analyzing the downloaded DLL and trying to gather more information from it. We’ll share more details about this malware later as we uncover more interesting details.
Mitigation
The original Word sample file has been detected as “WM/Agent.7F67!tr” by FortiGuard AntiVirus service.
IoCs
URL:
hxxps://sushi.vvlxpress.com:443/HA1QE
hxxps://pizza.vvlxpress.com:443/kH-G5
hxxps://pizza.vvlxpress.com:443/5MTb8oL0ZTfWeNd6jrRhOA1uf-yhSGVG-wS4aJuLawN7dWsXayutfdgjFmFG9zbExdluaHaLvLjjeB02jkts1pq2bR/
hxxps://sushi.vvlxpress.com:443/TtxCTzF1Q2gqND8gcvg-cwGEk5tPhorXkzS0gXv9-zFqsvVHxi-1804lm2zGUE31cs/
A Witch's Word Mac Os X
Sample SHA256:
Sample.doc 06A134A63CCAE0F5654C15601D818EF44FBA578D0FDF325CADFA9B089CF48A74

HA1QE.py 3A0924D55FB3BF3C5F40ADCE0BD281D75E62D0A52D8ADFA05F2084BA37D212C8
kH-G5.dll C36021A2D80077C2118628ED6DB330FEF57D76810FF447EF80D2AB35B95099BC
Sign up for weekly Fortinet FortiGuard Labs Threat Intelligence Briefs and stay on top of the newest emerging threats.